Learn Social Engineering From Scratch
Why take this course?
🚀 Learn Social Engineering From Scratch 🎓
Last Update: May 2024
Course Overview
Embark on a deep-dive into the world of social engineering with our comprehensive course, designed for beginners with NO PRIOR KNOWLEDGE in hacking. By the end of this course, you'll be equipped to perform advanced hacking techniques on Windows, Apple Mac OS, Linux, and Android. Plus, you'll learn how to defend yourself against such attacks!
Course Highlights:
- Practical Learning: Engage with hands-on exercises that bring theory to life without the boredom of lengthy lectures.
- Comprehensive Curriculum: From installing software to mastering advanced exploits, this course covers it all.
- Real-Life Scenarios: Learn by doing real-world hacking with practical examples and scenarios.
- Adaptability & Creativity: Gain the skills to modify techniques or combine them to create powerful, new attacks.
Course Breakdown:
-
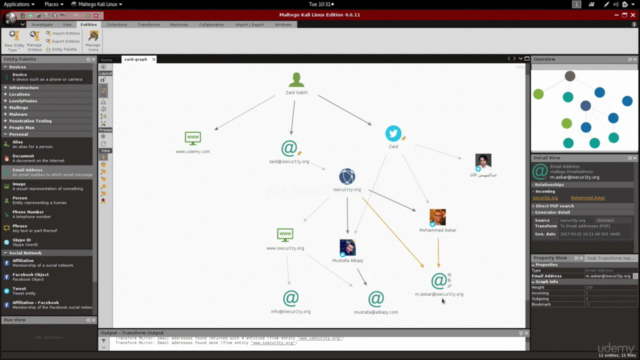
Information Gathering 🕵️♂️
- Understand how to collect vital information about your target, including websites, emails, and social networks.
- Plot this data on a graph to build smart attack strategies.
-
Generating Malware 🤫
- Create custom malware like backdoors, keyloggers, and credential harvesters that work across all major operating systems.
- Learn to bypass anti-virus programs and make your malware undetectable.
-
Delivery Methods 💌
- Master social engineering techniques to deliver your malicious code, including creating fake websites and sending phishing emails.
-
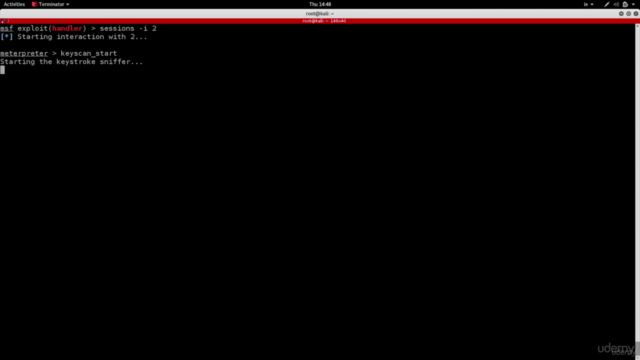
Post Exploitation 👀
- Access the file system, maintain access, escalate privileges, and monitor your target across different operating systems.
- If the target uses Android, learn to read messages, find their location, and access other accounts like WhatsApp and Facebook.
Additional Learning Perks:
- 24/7 Support: Have questions? We're here to help within 15 hours!
- Real-World Application: All practices are conducted in a secure lab environment or with devices you have explicit permission to test on.
Important Notes:
- This course is for educational purposes only and should not be used for illegal activities.
- The certification provided at the end of this course is from Udemy, and no other organization is associated with this content or a certification exam.
Dive into the detailed Curriculum and watch our Course Teaser to get a glimpse of what you'll learn in this extensive program! 💻🔍
Remember, knowledge is power, but with great power comes great responsibility. Use your newfound skills wisely and ethically! 🛡️✨
Course Gallery

Loading charts...
Comidoc Review
Our Verdict
<p>A comprehensive social engineering course from Zaid Sabih with real-world context, clear explanations, and practical assignments. However, there are concerns about the reliance on outdated tools and content duplication with other courses, making it essential to research recent developments in chosen areas prior to employing these techniques in real-life situations.<br><br>As evident by the global rating of 4.61, it has proven value for many learners interested in ethical hacking and penetration testing concepts. It should be noted that the focus of this Learn Social Engineering from Scratch 2024 course seems to be more on Windows and Linux platforms rather than a diverse showcase of social engineering attacks across all systems.<br><br>In summary, despite minor shortcomings, it is an insightful resource for gaining ethical hacking skills but should not serve as the only learning material in this subject area.<br></p>
What We Liked
- Highly detailed course covering a broad range of social engineering techniques and tools (12.5 hours)
- Excellent teaching style, with clear explanations and real-world context
- Practical assignments and attack simulations to reinforce learning
- Linux basics, command line usage, and overall sysadmin guidance
Potential Drawbacks
- Relies on outdated tools and examples from 2016 which may not work in practice today
- Content duplication with other courses, not solely focused on social engineering
- Limited emphasis on mobile devices and iOS platforms, more oriented towards Windows and Linux systems
- Mixed experiences reported for customer support